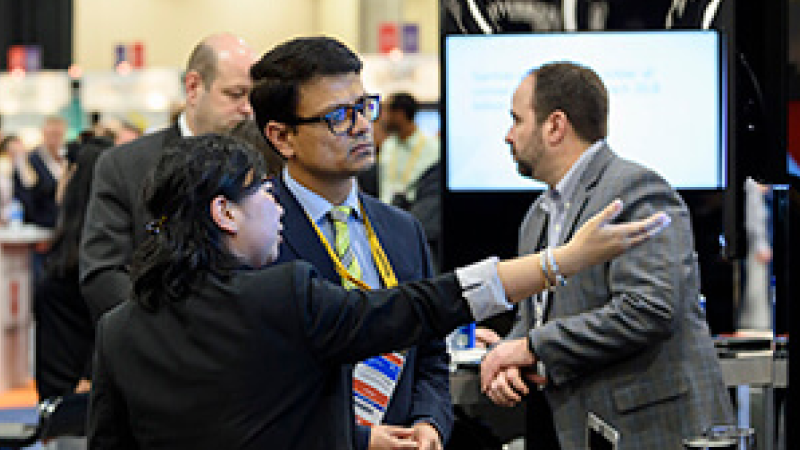
Visit the dynamic show floor, where you can interact with solution providers and learn about new products and services.
Premier
Hear peers share their experiences with solution providers:
“[Had a] great time connecting with old and new friends! Learned a lot and identified new product partners for our team. Exhibitors were amazing and [there were] so many newcomers.”
Jim Schiffer
Director, Identity Management, Freeport McMoRon