We are bringing you news and highlights from the Gartner Security & Risk Management Summit taking place this week virtually in EMEA and the Americas. Below is a collection of the key announcements, and insights coming out of the conference. You can also read the highlights here from Day 1 and Day 2.
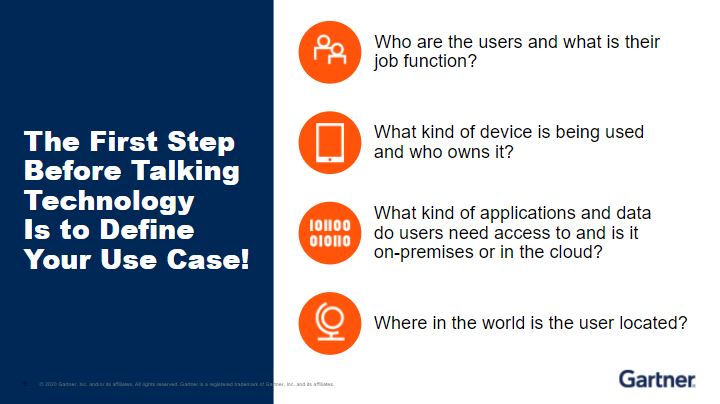
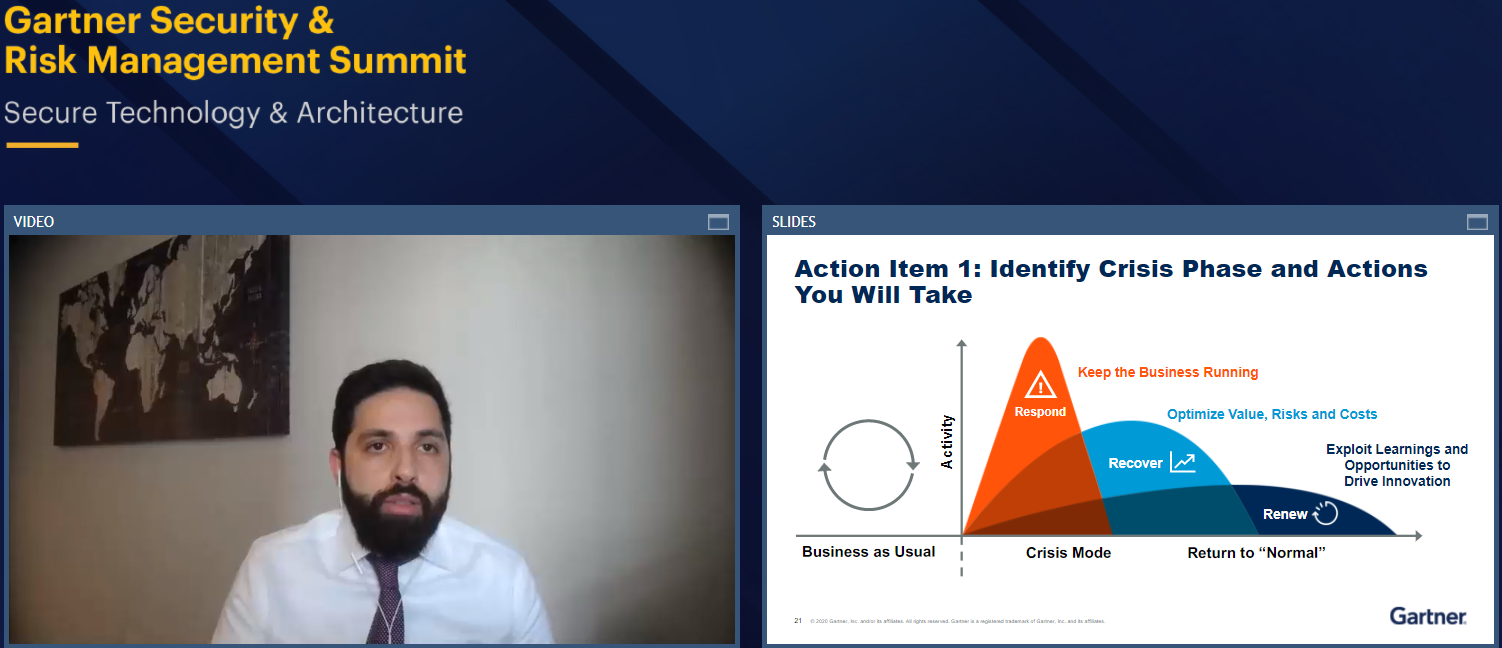
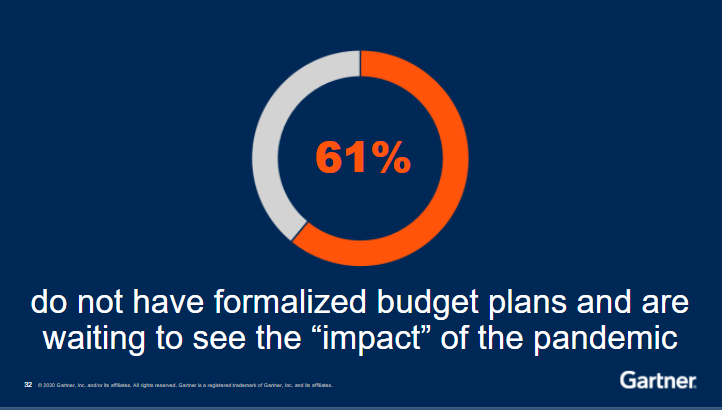
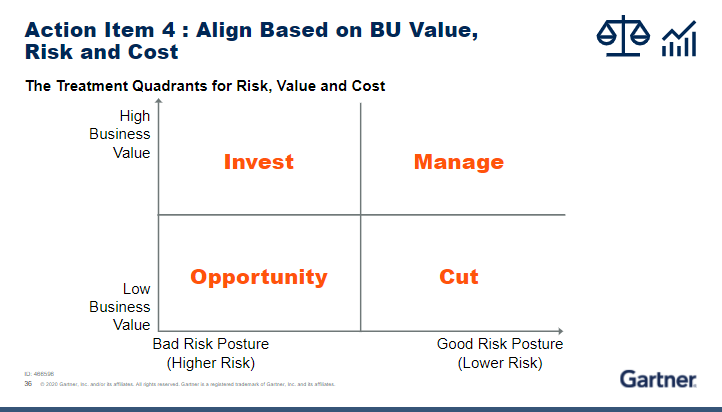
On Day 3 from the conference, we are highlighting how to solve the challenges of modern remote access in a post-COVID-19 world, followed by five cost optimization techniques for security & risk leaders, and the strategies for consistent security and compliance in a hybrid multicloud environment. Be sure to check this page throughout the day for updates.